Your SSN Isn't a Secret
Your Social Security Number is not supposed to be sensitive. It's an ID, nothing more. Unfortunately, more and more platforms and online systems use it to verify your identity.

No vulnerabilities were exploited and all information accessed was done with approval as part of this research.
Your Social Security Number is not supposed to be sensitive. It's an ID, nothing more. Unfortunately, more and more platforms and online systems use it to verify your identity, sort of like a password. However, in treating it as a password, we are placing consumers at a huge disadvantage.
Using your Social Security Number as a password is a bad idea. It would be an incredibly weak password and besides, you can't change it.
Let's quickly break down the Social Security Number.
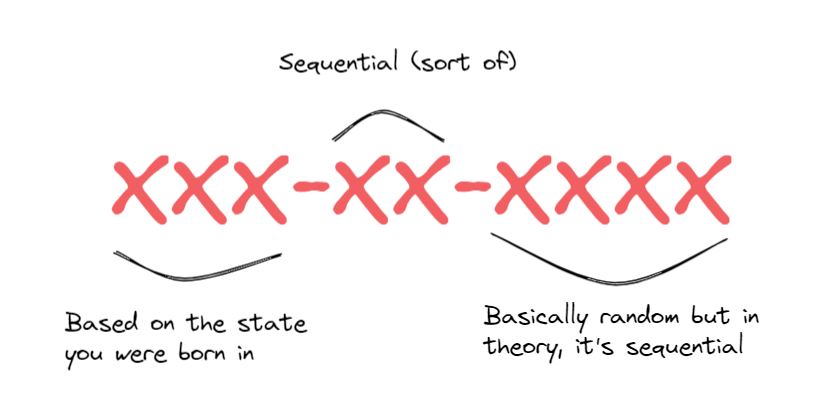
For example, if you were born in Minnesota, you probably recognize 467-477. In Montana, you might recognize 516-517.
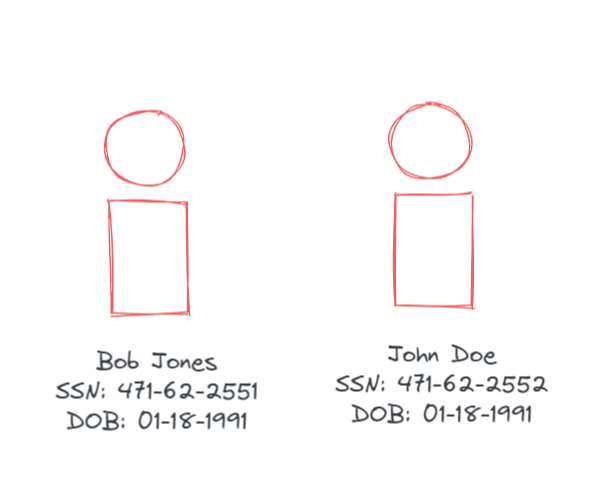
So based on that, there is possibly someone out there with the same birthdate, and an SSN incremented by one, two, or three.
Okay with that out of the way, let's get started.
Social Security Numbers are a highly regulated form of PII (Personally Identifiable Information). If your business collects SSNs, you'd better have a good reason for it, and you better keep them secure. Unfortunately, many large organizations allow anyone to access their cache of SSN's, providing you have an email.
Curious how this is done? Let's show you.
For this exercise, let's go with Morgan Stanley.
Let's say you're targetting an investment banker (for obvious reasons $$$). You know the name and the birthdate, those were found from a Google search.
Now, in order to gain access to the target's cell phone carrier, we need his SSN.
This common attack is called SIM swapping, in this scenario, an attacker calls a victim's cell phone carrier and switches the victim's phone number to a new SIM card. This allows the attacker to take over a phone number for further attacks.
In many cases, cell phone carriers use pin numbers to protect an account. Can you guess a common pin default pin number? That's right, the last four digits of the SSN.
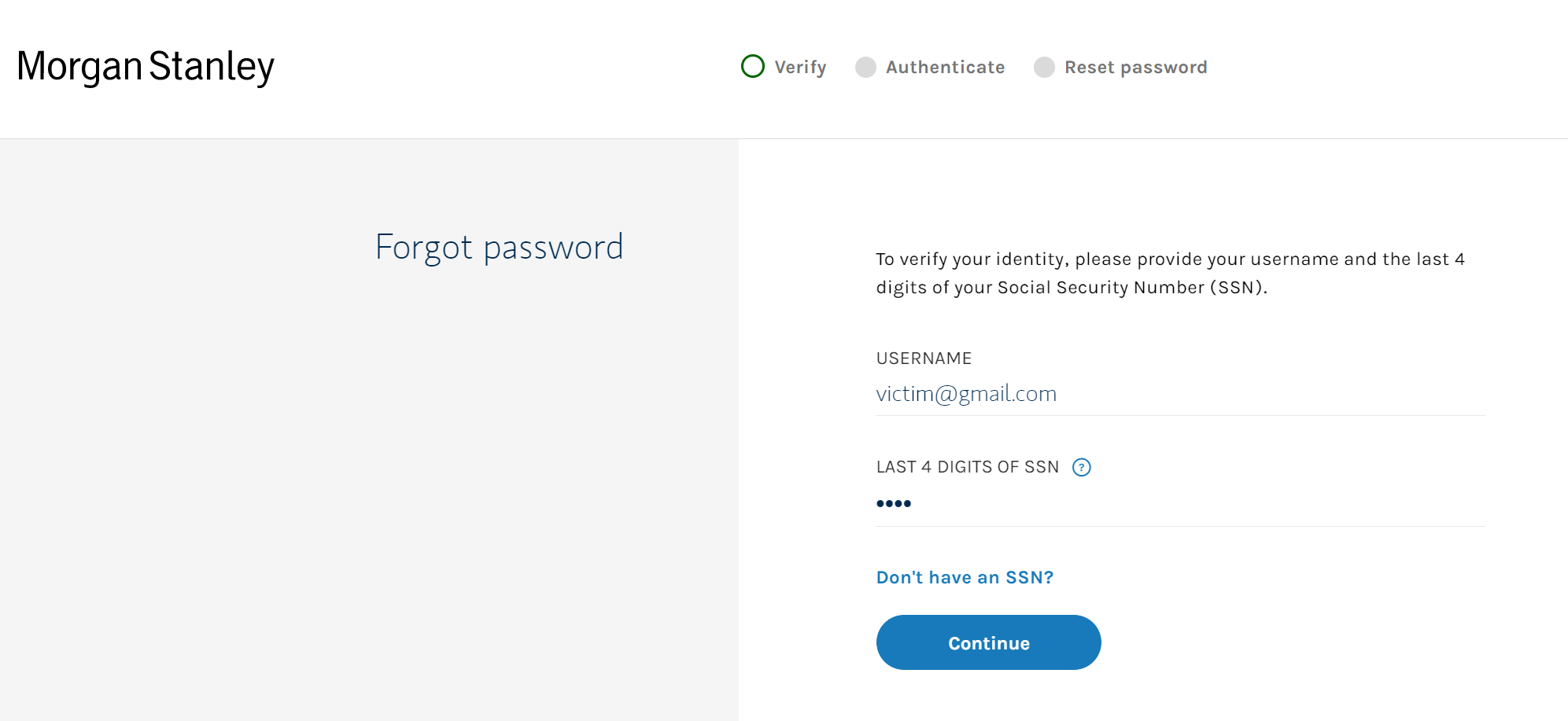
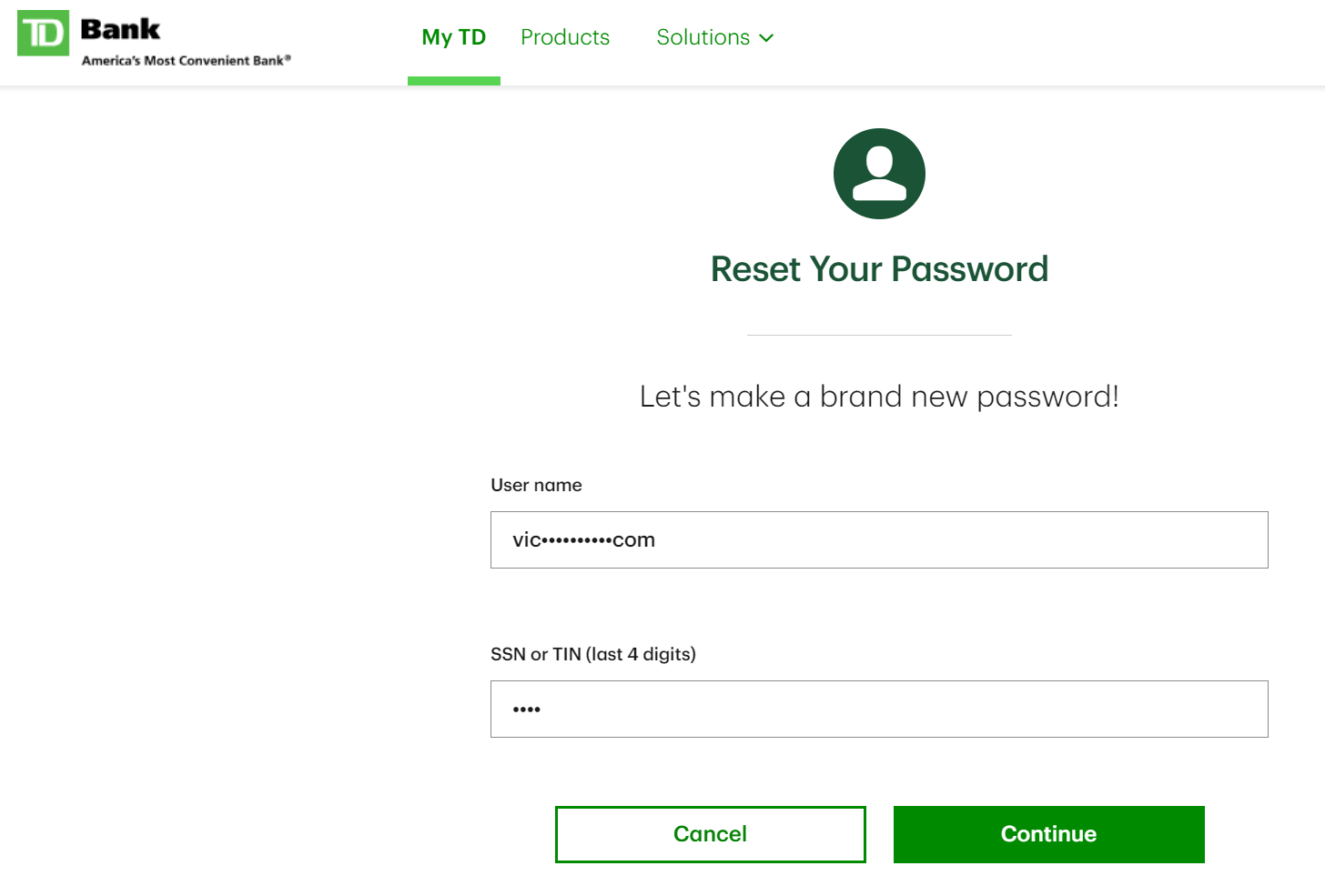
Using this portal, you can iterate through potential SSN's, or at least the last four digits. That's 10,000 possible combinations. Can anyone guess how fast a computer program can send 10,000 requests? Based on our tests, this shouldn't take more than 5 minutes.
When we submit a valid SSN, the response will indicate that a match was found.
Is this limited to Morgan Stanley? No.
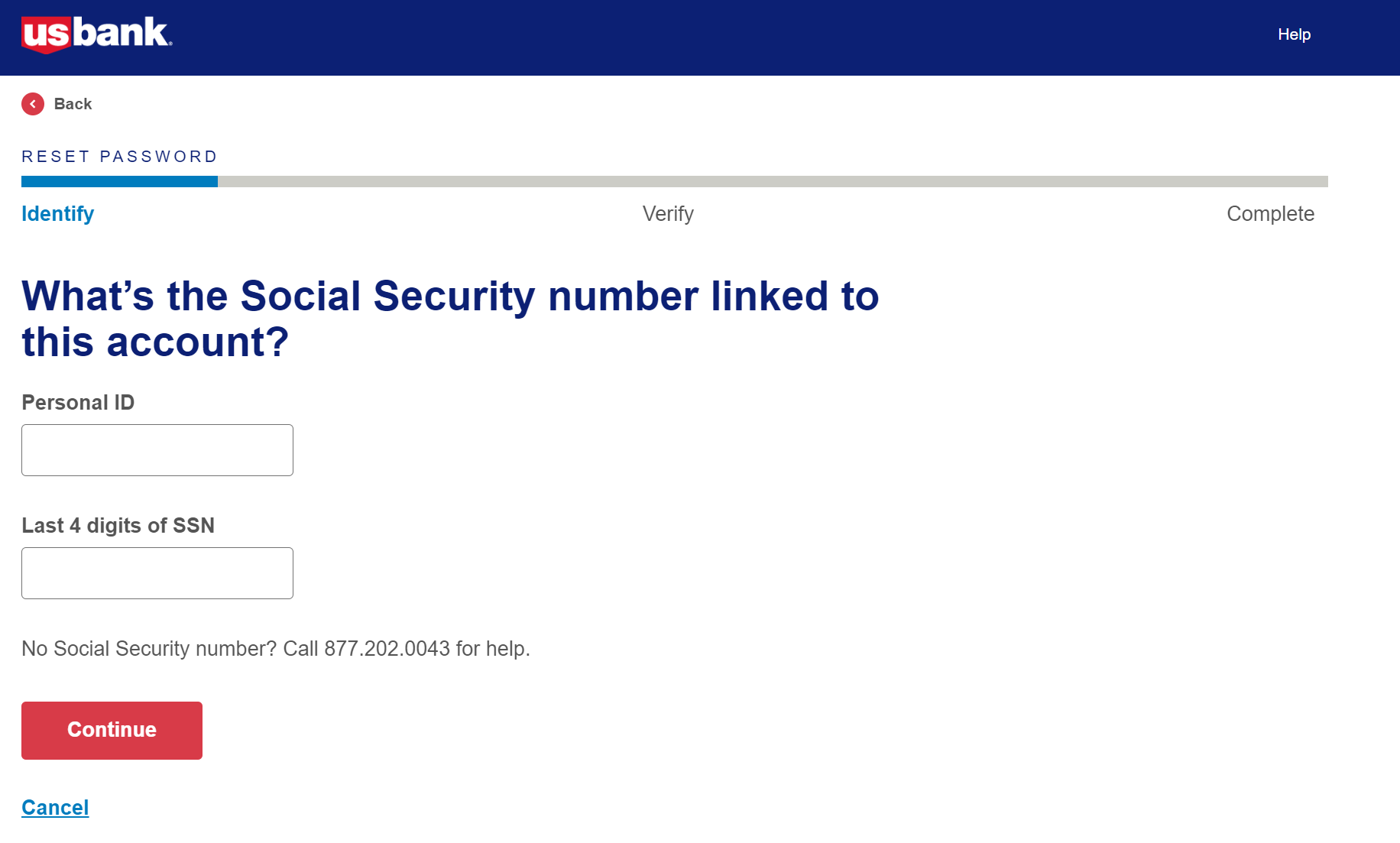
And the list goes on. Wells Fargo at least requests the entire SSN, however, this leads to its own set of issues.
Remember when we mentioned that similar SSNs are sequential? This is what happens when we take a known SSN, increment by one, and use the same DOB that is tied to the known SSN.
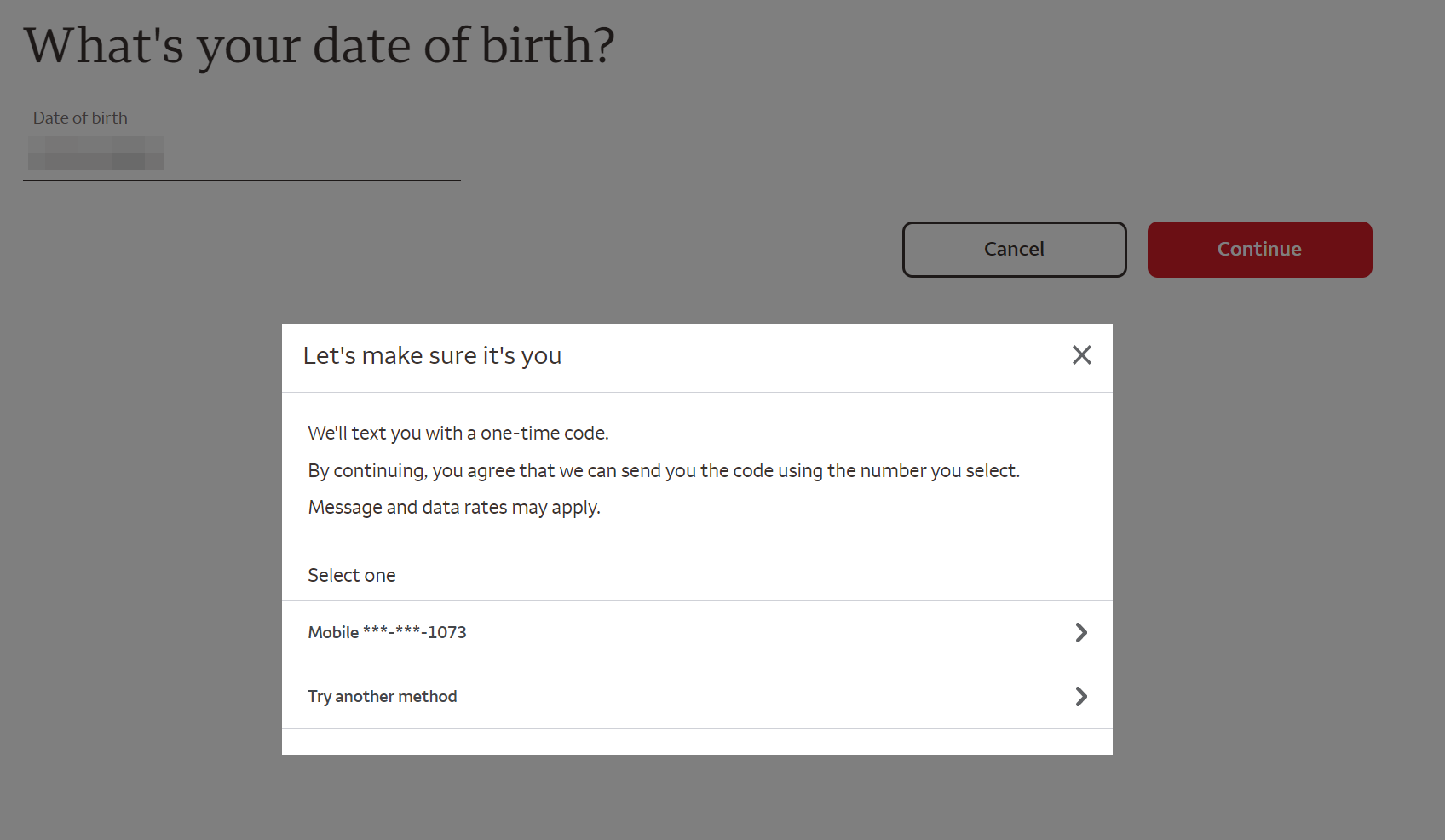
We get the last 4 digits of a phone number. Some Googling would likely turn up an address and full name. Of which, we already have an SSN.
So what can you do with the last four digits of an SSN?
Many systems using pin numbers default to the last four of your social. If it does not default, many people opt to use that since it's easy to remember.
Remember the last time you called Verizon, I bet they asked for your pin. Same with many utility companies and insurance companies.
What can you do about it?
For starters, don't panic. Beyond the methods explained here, your SSN may well be for sale on the dark web.
Adversis wants you to be informed. Use this knowledge when making decisions regarding your SSN going forward.
When possible, change your pins to something other than your social.
Use unique email addresses for different services. Did you know you can add a plus to your Gmail addresses?
For example, let's say your email is [email protected]. You can sign up for services with [email protected] and still receive emails. This is also handy for determining which online services are sending you spam.
If you're still worried, you can always freeze your credit.
As of 2011, social security numbers are randomized so anyone born after that point will not have predictable SSN's.
Get in touch today!
Contact: [email protected]
Adversis: https://adversis.io
Adversis ACS: https://acs.adversis.io


